Lines of Light: a book review
Lines of Light is a graphic novel by Dan Nott, which examines the “history and geography of the internet.” I was fortunate enough to meet the author at the Massachusetts Independent Comic Expo, which was held at Lesley University. This quarter I am teaching two courses on related topics (Digital Globalization as well as CyberWar and Espionage), so I was curious to view this work. This graphic novel is exceptional not only because it is visually engaging, but also because it takes a completely unexpected view of something that we all assume we understand. With his clear, concise prose to describe a physical world that we all rely upon, this book is filled with unexpected facts and insights.
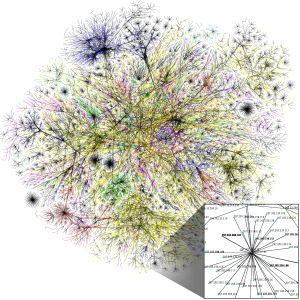
One of the approaches that Nott takes is too look at how we use metaphors to talk about the internet, which can sometimes be misleading. The book starts with Senator Ted Stephens at the net neutrality hearing of 2006, where he tried too use a failed metaphor to describe the internet. From this moment, the work moves to consider more broadly how we all talk about the internet, and how accurate that language may be. While it might be easy to mock Senator Stephens, most of us also wrestle to describe something so abstract. Nott’s brilliance is being able to take these metaphors and place them into both a historical and a physical context, which is grounded by the detailed maps and imagery of the infrastructure that supports the internet. …